February 2010 - Vol. 53 No. 2

Features
Connecting Women and Technology
Alternate Interface Technologies Emerge
Not Seeing the Crime For the Cameras?
The Need For a National Cybersecurity R&D Agenda
Open Access to Scientific Publications
Taking Your Network’s Temperature
An Interview with Michael Rabin
Managing Contention For Shared Resources on Multicore Processors
Software Model Checking Takes Off
A Few Billion Lines of Code Later: Using Static Analysis to Find Bugs in the Real World
Assessing the Changing U.S. IT R&D Ecosystem
Recent Progress in Quantum Algorithms
Technical Perspective: Strange Effects in High Dimension
Technical Perspective: Want to Be a Bug Buster?
Post-Silicon Bug Localization For Processors Using IFRA
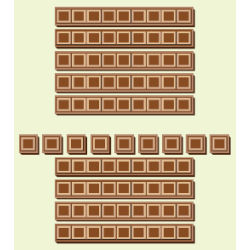
Puzzled: Breaking Chocolate Bars
Reversing the Landslide in Computer-Related Degree Programs
Wireless Insecurity: Examining User Security Behavior on Public Networks
Taking a Flexible Approach to ASPs
Informatics Creativity: A Role For Abductive Reasoning?
Practical Intelligence in IT: Assessing Soft Skills of IT Professionals
Managing a Corporate Open Source Software Asset
It Takes Two to Tango: How Relational Investments Improve IT Outsourcing Partnerships