Technology Has Social Consequences
May 2011 - Vol. 54 No. 5

Features
Preserve Privacy in Statistical Correlations
Stonebraker on Data Warehouses
Let ACM Help You Find Your Next Job ‘Online’
Data Optimization in Developing Nations
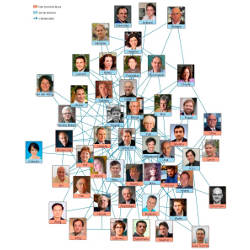
Web Science Meets Network Science
Online Advertising, Behavioral Targeting, and Privacy
Reaching Learners Beyond Our Hallowed Halls
Bell Labs and Centralized Innovation
An Interview with Steve Furber
The Importance of Reviewing the Code
Mobile Application Development: Web vs. Native
Brain-Computer Interfaces For Communication and Control
Privacy-Preserving Network Forensics
Technical Perspective: Complex Financial Products: <i>Caveat Emptor</i>
Computational Complexity and Information Asymmetry in Financial Products
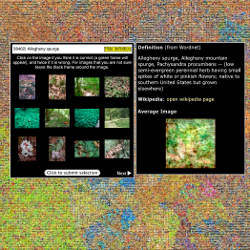
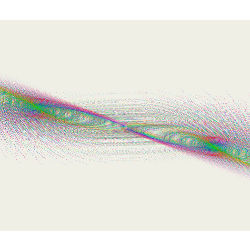
Technical Perspective: Images Everywhere Looking For Models
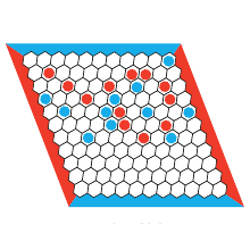
Self-Similarity-Based Image Denoising
Challenges and Business Models For Mobile Location-Based Services and Advertising
Is Open Source Security a Myth?
Invisible Work in Standard Bibliometric Evaluation of Computer Science