Computer Science Curricula 2013 Released
June 2014 - Vol. 57 No. 6

Features
The Computer Science Curricula 2013 was released last fall with the goal of providing advice and guidance to the computing education community throughout the coming decade.
Opinion Letter from the President
While ACM is deeply dependent on the extraordinary contributions of our volunteers, the organizational framework and underlying support for this work is key to ACM's successful operation.
Opinion Letters to the Editor
Efficient Code to Counter Dying Moore’s Law
If Moore's Law is indeed winding down, as Moshe Y. Vardi said in "Moore's Law and the Sand-Heap Paradox" (May 2014), software practitioners must focus even more than they already do on developing efficient code.
First Impressions, Unexpected Benefits
Daniel Reed shares his experiences with Google Glass, while Chris Stephenson considers the kinds of support chapters of the Computer Science Teachers Association provide their members.
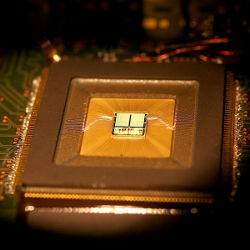
Neuromorphic Computing Gets Ready For the (Really) Big Time
A technology inspired by biological principles but 'steamrolled for decades' prepares to take off as Moore's Law approaches its long-anticipated end.
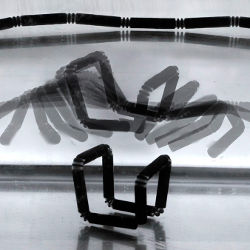
4D printing combines the dimension of time with the hope of building objects with new capabilities.
Visualizations Make Big Data Meaningful
New techniques are designed to translate "invisible numbers" into visible images.
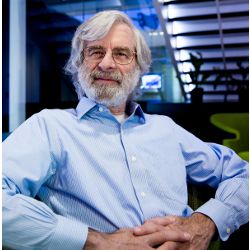
Leslie Lamport contributed to the theory and practice of building distributed computing systems that work as intended.
Opinion Inside risks
What lessons might we learn from the chip cards used for payments in Europe, now that the U.S. is adopting them too?
Opinion Privacy and security
Relying on dubious claims can cause researchers to focus on the wrong questions and organizations to misdirect security spending.
Opinion The profession of IT
Computing technology has generated conditions for radical transformations of jobs and professions — including education. How shall we cope?
Opinion Viewpoint
Why business analytics and big data really matter for modern business organizations.
Research and Advances Contributed articles
EPIC helps assess cyberthreats against the cyber and physical dimensions of networked critical infrastructures.
Research and Advances Contributed articles
The Power of Social Media Analytics
How to use, and influence, consumer social communications to improve business performance, reputation, and profit.
Research and Advances Contributed articles
The Digitization of Cultural Practices
These interactive applications let users perform, and thus preserve, traditional culture-defining crafts.
Research and Advances Review articles
Implementing Distributed Shared Memory For Dynamic Networks
Atomically consistent memory services provide resiliency in dynamic settings.
Research and Advances Research highlights
Technical Perspective: Motion Fields For Interactive Character Animation
The following paper effectively treats motion clips as a set of independent motion vectors. In their ensemble, these high-dimensional motion vectors define a motion field that governs how the state of a character evolves over time.
Research and Advances Research highlights
Motion Fields For Interactive Character Locomotion
We propose a novel representation of motion data and control of virtual characters that gives highly agile responses to user input and allows a natural handling of arbitrary external disturbances.
Opinion Last byte
Puzzled: Solutions and Sources
Last month (May 2014) we posted three puzzles in which you were asked to sort several cards using three stacks on a table.
Opinion Last byte
Leslie Lamport on Byzantine generals, clocks, and other tools for reasoning about concurrent systems.