November 2012 - Vol. 55 No. 11

Features
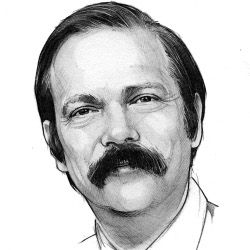
When Predicting, Start With Humility
Major Update to ACM’s Computing Classification System
The Research Value of Publishing Attacks
Oracle v. Google: Are APIs Copyrightable?
Decentralization Versus Centralization in IT Governance
Learning to Teach Computer Science: The Need For a Methods Course
Societal Implications of the Emerging Smart Grid
Resilience Engineering: Learning to Embrace Failure
Disks from the Perspective of a File System
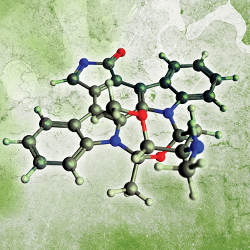
Functional Encryption: A New Vision For Public-Key Cryptography
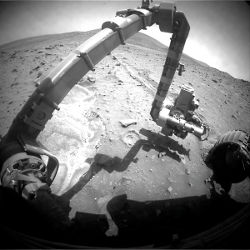
The Challenges Ahead For Bio-Inspired ‘Soft’ Robotics
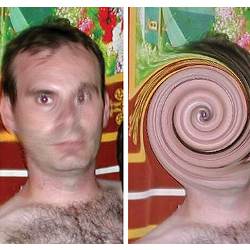
Technical Perspective: Open Platforms For Computational Photography
The Frankencamera: An Experimental Platform For Computational Photography
Technical Perspective: The Realities of Home Broadband
Measuring Home Broadband Performance
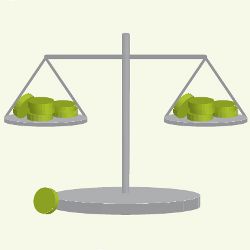
Puzzled: Weighed in the Balance