September 2011 - Vol. 54 No. 9
Features
Solved, For All Practical Purposes
Jeannette M. Wing @ PCAST; Barbara Liskov Keynote
A Breakthrough in Algorithm Design
In Praise of ‘Wilkes, Wheeler, and Gill’
Corporate Social Responsibility and Global IT Outsourcing
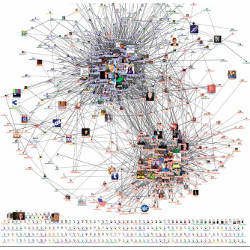
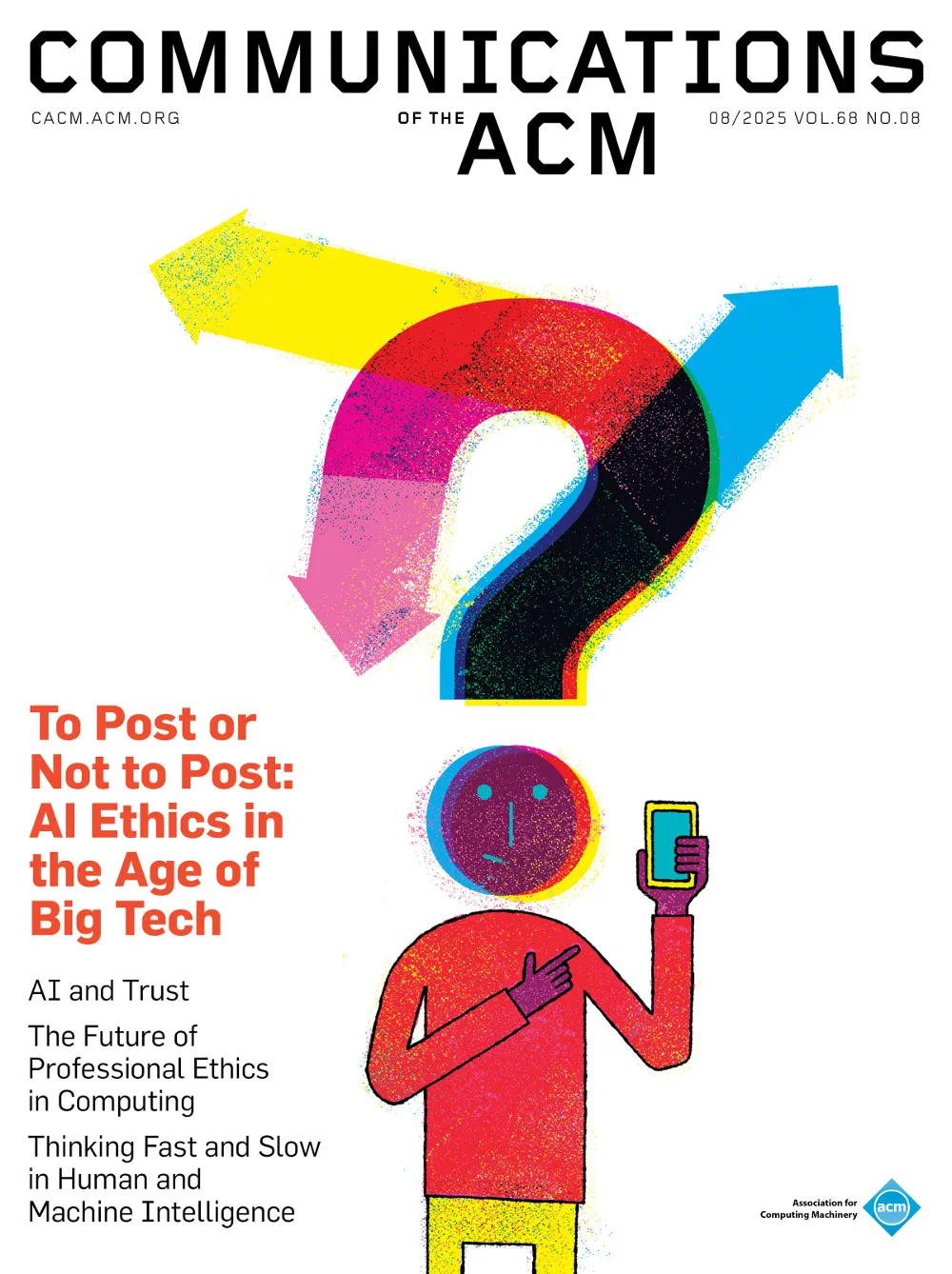
Realizing the Value of Social Media Requires Innovative Computing Research
The Most Expensive One-Byte Mistake
ACM CTO Roundtable on Mobile Devices in the Enterprise
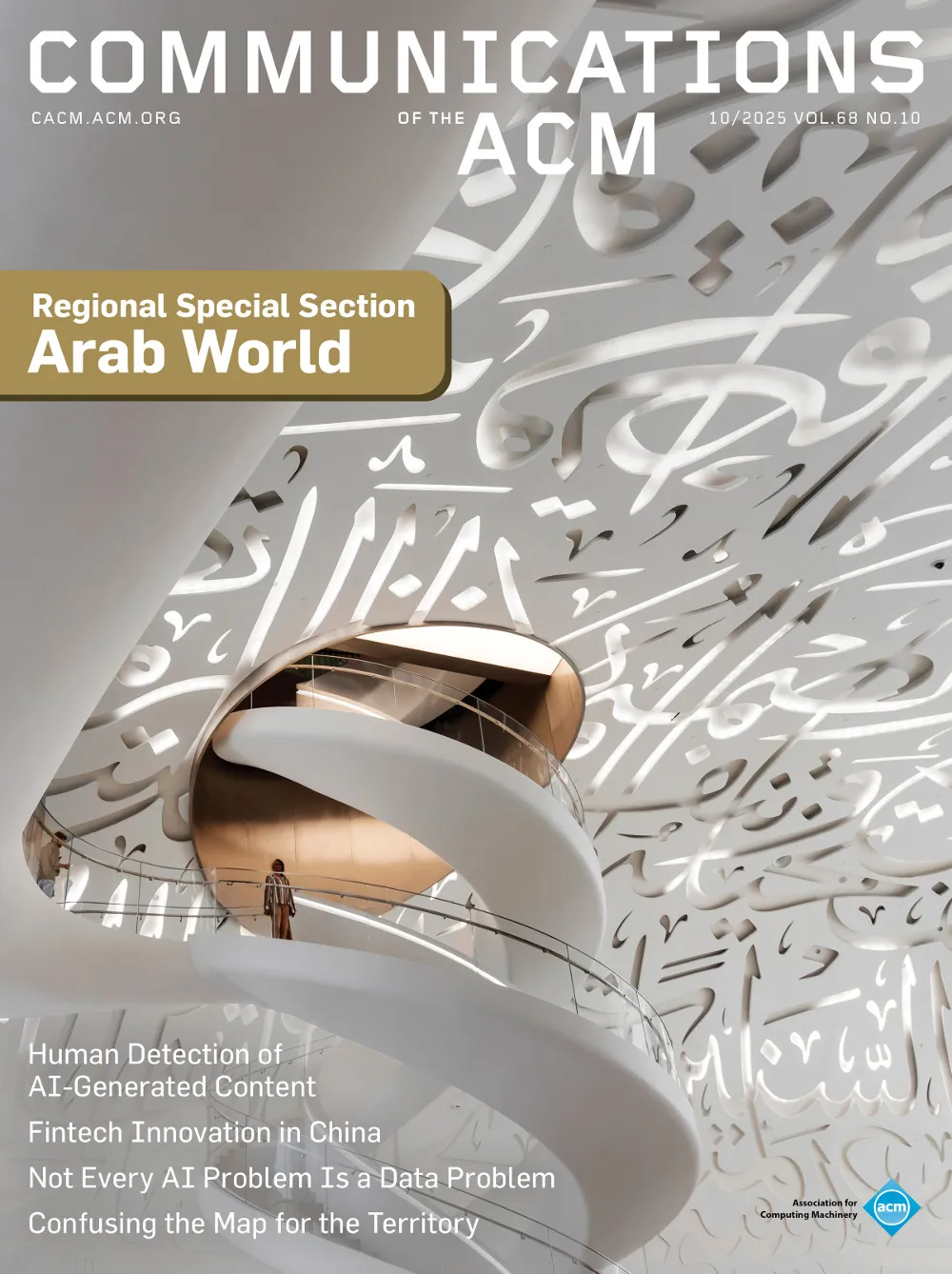
Protecting Users of the Cyber Commons
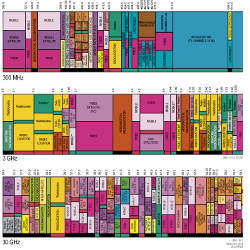
Realizing the Future of Wireless Data Communications
Satisfiability Modulo Theories: Introduction and Applications
Quantitative Analysis of Real-Time Systems Using Priced Timed Automata
Technical Perspective: Making Browser Extensions Secure
Vetting Browser Extensions For Security Vulnerabilities with VEX
Technical Perspective: Abstracting Abstract Machines
Abstracting Abstract Machines: A Systematic Approach to Higher-Order Program Analysis
Puzzled: Solutions and Sources
Crossing to the Dark Side: Examining Creators, Outcomes, and Inhibitors of Technostress
Calculating and Improving ROI in Software and System Programs