November 2011 - Vol. 54 No. 11

Features
In Support of Open Reviews; Better Teaching Through Large-Scale Data Mining
ACM Offers a New Approach to Self-Archiving
Security Risks in Next-Generation Emergency Services
Why the Google Book Settlement Failed – and What Comes Next?
Will Software Engineering Ever Be Engineering?
Teaching-Oriented Faculty at Research Universities
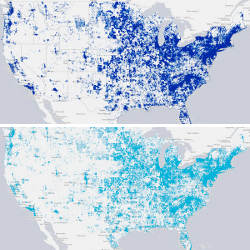
Gender Demographics Trends and Changes in U.S. CS Departments
Java Security Architecture Revisited
‘Natural’ Search User Interfaces
Managing Is Adoption in Ambivalent Groups
The Rise and Fall of High Performance Fortran
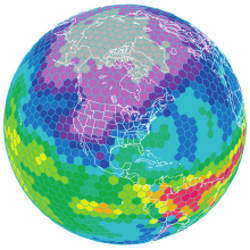
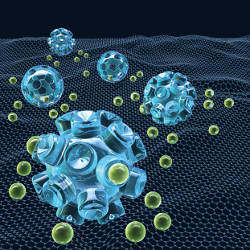
Nanonetworks: A New Frontier in Communications
Technical Perspective: Making Untrusted Code Useful
Making Information Flow Explicit in HiStar
Technical Perspective: A Perfect ‘Match’
The Patchmatch Randomized Matching Algorithm For Image Manipulation
Puzzled: Distances Between Points on the Plane
Information Seeking: Convergence of Search, Recommendations, and Advertising