A growing reliance on generative AI search has many worried that website traffic and clicks could fall off a cliff.
News
GenAI: The Buy vs. Build Solution
The rush to embrace AI can lead to ill-considered decisions that can come back to haunt an organization.
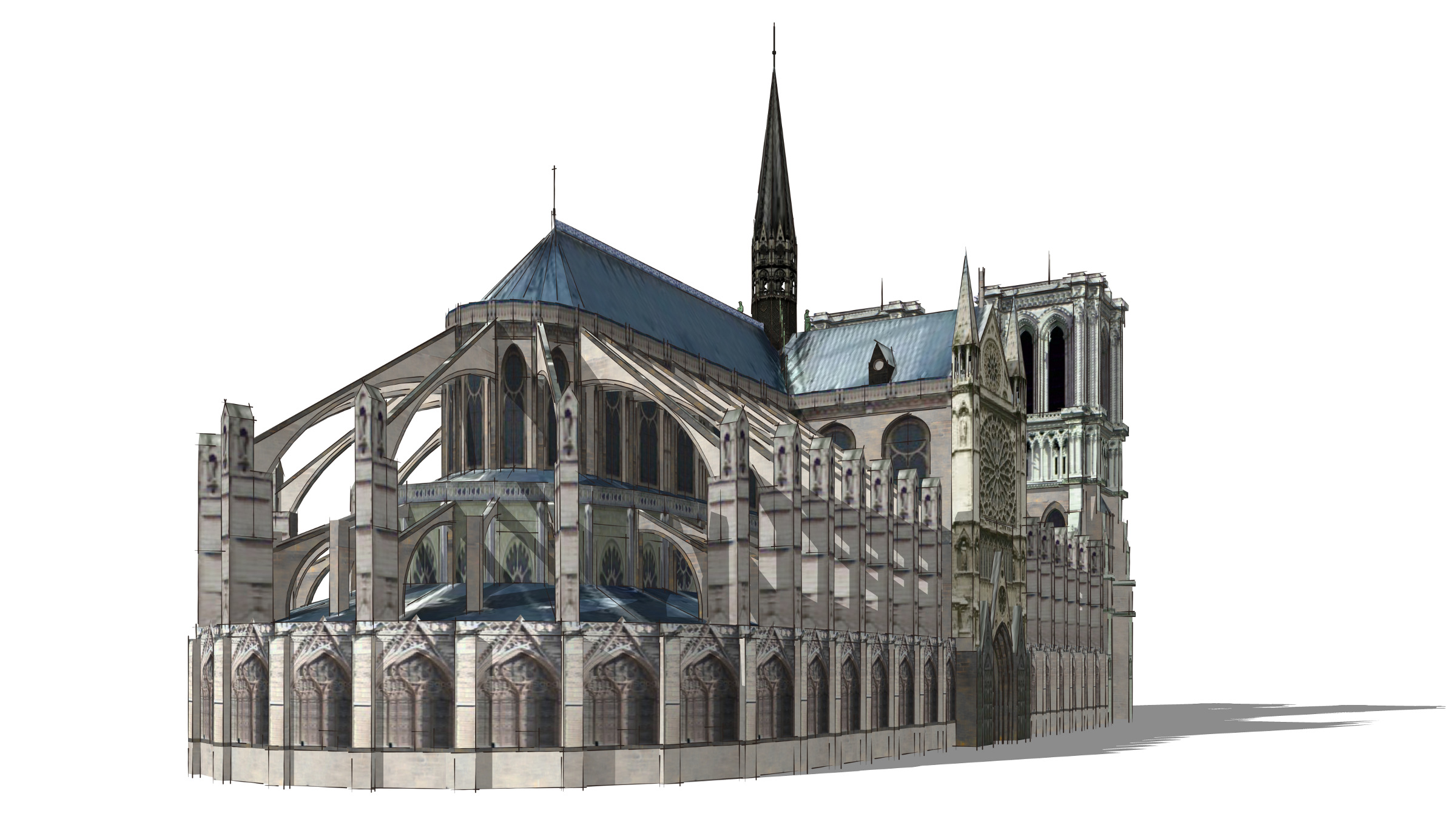
Creating Digital Replicas of History with AI
AI-assisted renderings can show historic structures in precise detail across different time periods.
Verification Systems Face an Identity Crisis
Artificial intelligence is making common digital defense tools obsolete.
You Deserve Some Cybersecurity Today
McDonald's said it was committed to cybersecurity and to holding third-party vendors to high data protection standards.
The Challenges of Fusion-Based Electricity for AI Datacenters
With industrial-scale energy appetites, AI datacenters are the steel mills of the modern era.
Overcoming Obstacles to Passwordless Authentication
Organizations need the proper skills and teams to implement passwordless authentication effectively.
AI is increasingly being used in kitchens and restaurants to push the boundaries of what’s possible in the culinary arts.
Securing Japan from Online Attacks
Can AI Help Build Cities Better?
Planners hope that the right balance of automation and human accountability will contribute to more livable and sustainable urban environments.
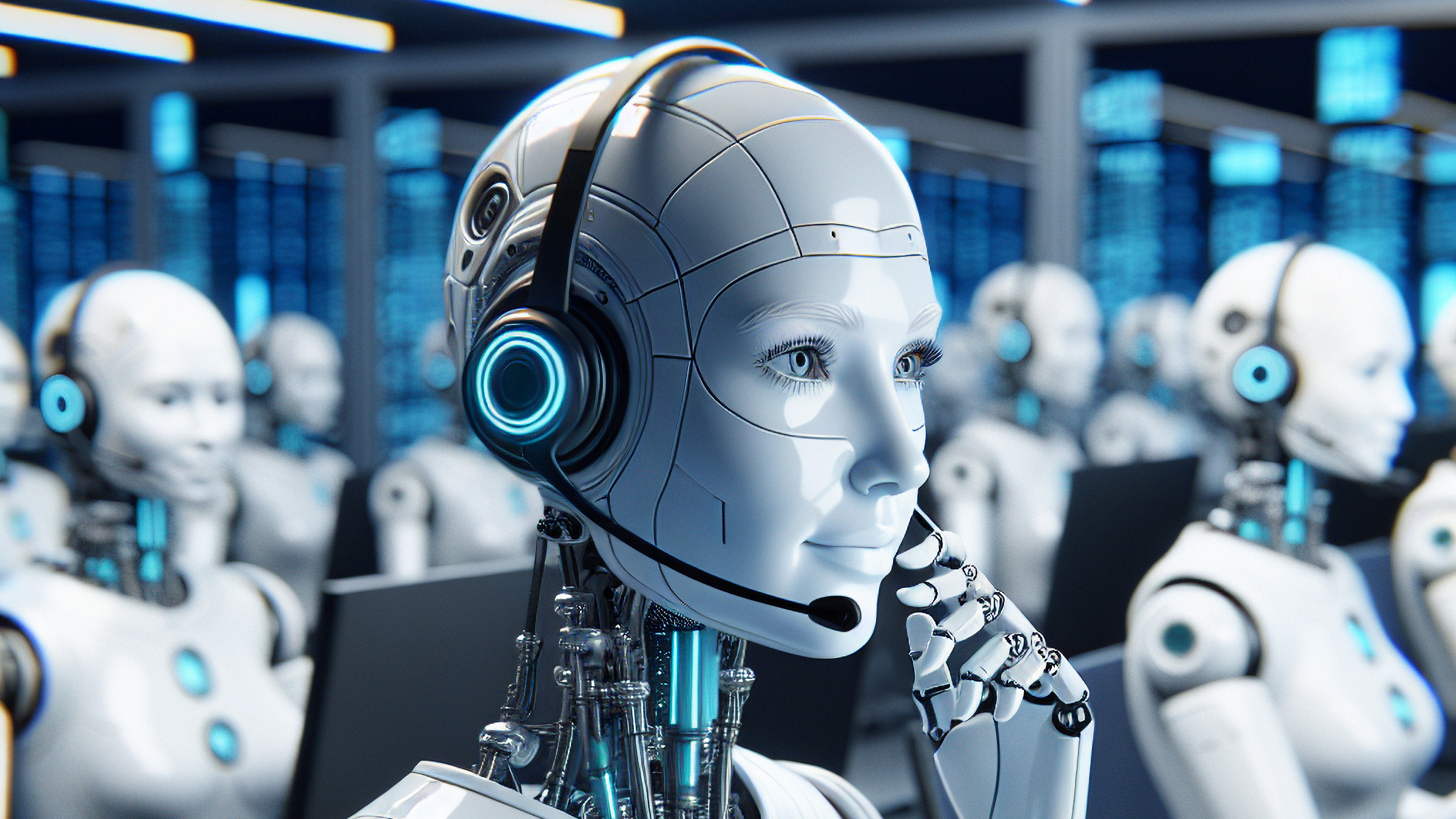
Automating Call Centers with AI
Even people in the contact center industry support the use of AI, potentially at the expense of their own jobs.
Recent research holds some clues as to which jobs are being affected by AI and shows signs of how that is playing out in the jobs markets.
Scientists are using machine learning techniques such as classifiers to identify units of language and hope deep neural networks will help them figure out what animals might be talking about.
AI Datacenters Need Nuclear Fusion
Fusion reactors may answer the question of where energy for AI datacenters will come from.
Juice jacking requires attackers to tamper with a public USB charging station to load malicious software that would open a device to two-way data transfer.
AI may be adding a new layer to the cognitive processes that go into human decision making.
Language Models Wrestle with Gaps in Understanding
Bigger language models tend to use the first half of their layer stack to extract a single fact, no matter how many layers they have available in total.
Some AI labs support digital watermarking to indicate whether an image is generated by an AI tool.
How Far Away Is Quantum Supremacy?
Two big obstacles stand between current quantum computers and the hardware needed for business use cases.
Improving Everyday Computer-Human Interactions
Solutions presented in several papers at CHI 2025 may not be as simple to implement as they sound, experts say.
The Pros and Cons of Zero Trust
Implementations are complex, resource-intensive, and involve high costs.
AI’s Benefits Can Be Marginal in Medicine
The perception of AI driving magical medical breakthroughs is often far from the truth.
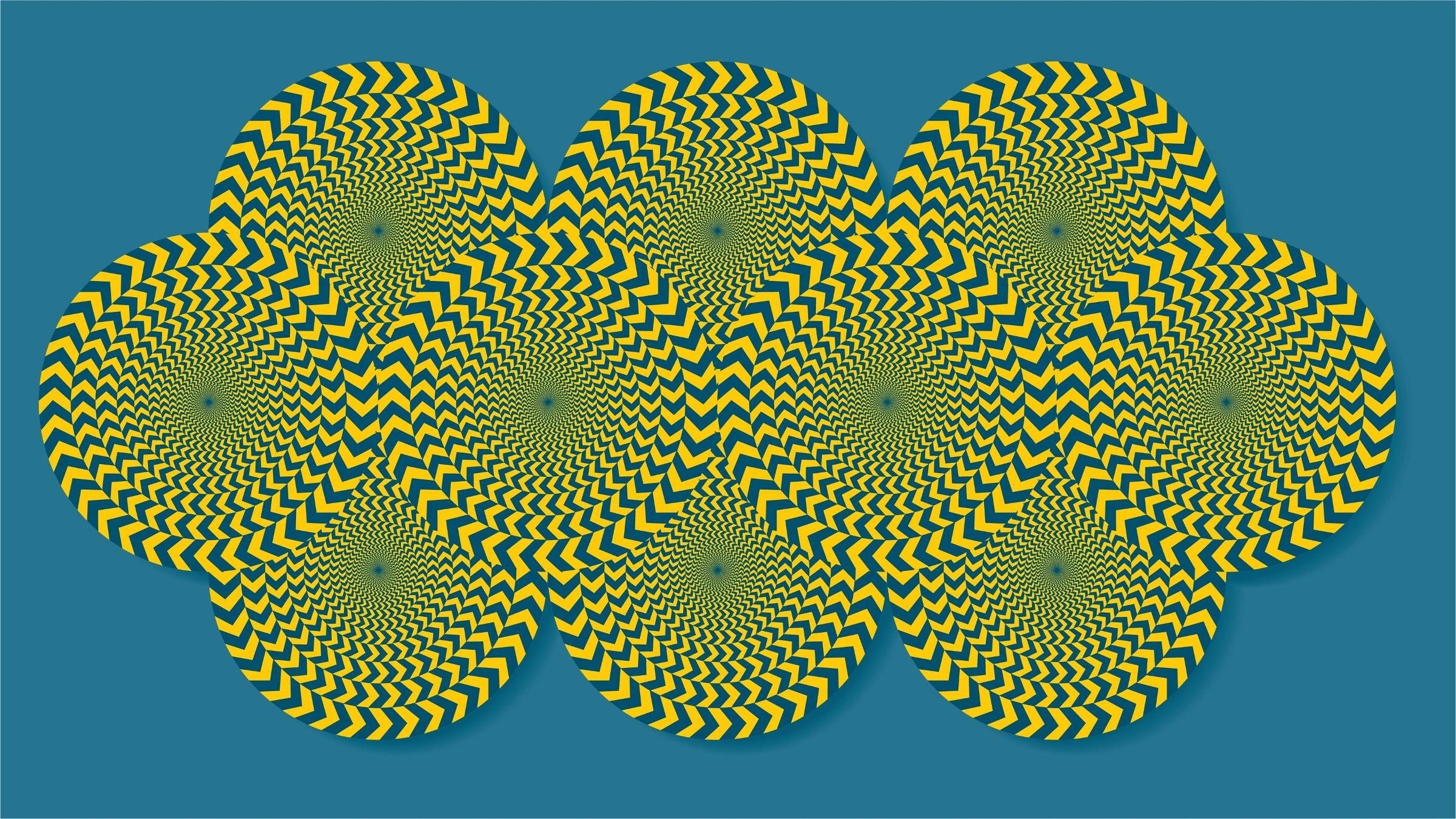
Illusions provide a way to study compositional generation and understand how machine learning models generate images.
Shape the Future of Computing
ACM encourages its members to take a direct hand in shaping the future of the association. There are more ways than ever to get involved.
Get InvolvedCommunications of the ACM (CACM) is now a fully Open Access publication.
By opening CACM to the world, we hope to increase engagement among the broader computer science community and encourage non-members to discover the rich resources ACM has to offer.
Learn More