How ACM Is Adapting in This Period of Global Uncertainties
May 2020 - Vol. 63 No. 5

Features
Partnerships Can Help Drive Gender Equality
Efficiency vs. Resilience: What COVID-19 Teaches Computing
Launching a New Feature in Communications
Automating Automation: CS at the Heart of the Manufacturing Economy
Teaching CS Humbly, and Watching the AI Revolution
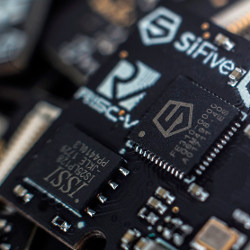
Will RISC-V Revolutionize Computing?
Deceiving the Masses on Social Media
What Role for Antitrust in Regulating Platforms?
A Vision of K-12 Computer Science Education for 2030
Computers Do Not Make Art, People Do
Revealing the Critical Role of Human Performance in Software
Reading in the Panopticon: Your Kindle May Be Spying on You, But You Can't Be Sure
A Bibliometric Approach for Detecting the Gender Gap in Computer Science
A Snapshot of the Frontiers of Fairness in Machine Learning
Technical Perspective: Fake ‘Likes’ and Targeting Collusion Networks
Measuring and Mitigating OAuth Access Token Abuse by Collusion Networks