New Ways to Think About CS Education
April 2020 - Vol. 63 No. 4
Features
Adding More Color to Patch Picture
Teaching Teachers to Offer STEM to Undergrads
Machine Learning, Meet Whiskey
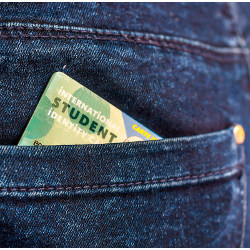
How Universities Deploy Student Data
The Temptation of Data-Enabled Surveillance
Artificial Intelligence and the Future of Professional Work
Why Is Cybersecurity Not a Human-Scale Problem Anymore?
Organizing Family Support Services at ACM Conferences
A Taxonomy of Automated Assistants
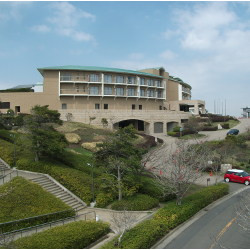
The NII Shonan Meeting in Japan
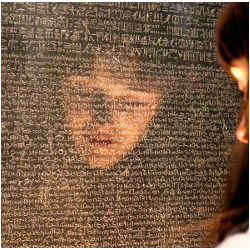
Capturing Cultural Heritage in East Asia and Oceania
Cybersecurity in Pacific Island Nations
Singapore’s Cybersecurity Ecosystem
Innovating Services and Digital Economy in Singapore
AI Singapore: Empowering a Smart Nation
Developing AI for Law Enforcement in Singapore and Australia
Digital Healthcare Across Oceania
Detecting Fake News in Social Media: An Asia-Pacific Perspective
seL4 in Australia: From Research to Real-World Trustworthy Systems
Advances in Security Research in the Asiacrypt Region
5G Commercialization and Trials in Korea
Asia’s Surging Interest in Binary Analysis
Managing the Hidden Costs of Coordination
Cognitive Work of Hypothesis Exploration During Anomaly Response
Cyber Warranties: Market Fix or Marketing Trick?
Technical Perspective: An Answer to Fair Division’s Most Enigmatic Question
A Bounded and Envy-Free Cake Cutting Algorithm