The summer of 2017 saw two Chinese projects demonstrate the potential to move encryption based on quantum techniques from small-scale trials into networks that can span the globe.
The completion of an $85-million fiber-optic network that runs 1,200 miles from Beijing to Shanghai through Jinan and Hefei marks a distance record for quantum key distribution (QKD). Designed to overcome a fundamental problem in conventional cryptography—how to transmit a private encryption key securely to another user without risk of it being intercepted—QKD has until recently been limited to networks that span no more than a few hundred miles.
As the Beijing-Shanghai link started to transmit QKD-protected data, another team based in China reported the successful use of a satellite to transfer similarly encrypted data transferred between ground stations 750 miles apart.
Grégoire Ribordy, CEO of Geneva, Switzerland-based ID Quantique, says of the satellite experiment, “Everybody in the science field knew it was possible, but there is a difference between knowing and seeing a demonstration. This is a technology that makes possible global QKD networks.”

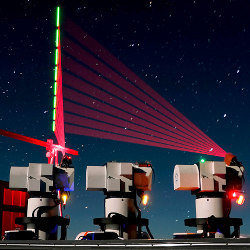
Figure. This composite photo taken on Dec. 10, 2016 shows a quantum communication ground station in southwest China’s Tibet Autonomous Region.
The concept underpinning QKD is now more than half a century old, although it spent the first 20 years in obscurity. The original proposal was rejected by editors working on a journal published by the Institute of Electrical and Electronics Engineers (IEEE) in the 1970s. It was resurrected as the basis for a protocol devised by Charles Bennett and Gilles Brassard and presented at a 1984 IEEE conference on signal processing in New York.
The BB84 protocol uses the Heisenberg uncertainty principle, which argues measuring one part of a quantum state makes it impossible to determine other linked properties. Many BB84-based schemes use polarized light for this purpose. If a polarizer is aligned at angle of 45°, there is a 50% probability of the photon passing through being detected. Even so, its polarization is irrevocably realigned so further measurements cannot reveal its original state.
If the alignment is known, an eavesdropper can easily interpose their own detectors and copy the photon states successfully. But if the sender randomly switches alignments between perpendicular and angled positions, the eavesdropper has to guess correctly to be sure of passing the correct state on to the receiver. The QKD protocol has the sender and receiver check with each other which bits were transmitted successfully. If there are no physical weaknesses in the equipment used, the users can perform the check without disclosing bits in the final key. A low success rate for tested bits indicates an eavesdropper is present; at that point the parties can decide to try again or use a different channel.
Although the basic BB84 protocol relies on the ability to detect eavesdropping, variants of the protocol remove this requirement. In 2014, researchers at Toshiba designed a protocol that uses a second wave of selection on the sifted bits to yield a key that, under available technology, is guaranteed to be secure.
Numerous experiments into QKD have been conducted since the early 2000s to test the technology’s reliability and performance. Ribordy says 2017 marked the 10th anniversary of the first use of QKD to protect voting data in elections in the company’s home country of Switzerland. He says, as found by the Chinese project, banks have been the primary early adopters of QKD, typically to support the backup of data between nearby datacenters.
2017 marked the 10th anniversary of the first use of quantum key distribution to protect voting data in elections in Switzerland.
The main problem with QKD is its range; photons are readily absorbed in long-distance fiber. The problem is less acute with atmospheric transmissions, as the satellite experiment demonstrated, but the losses increase exponentially in the time it takes to successfully send a single key bit, as they do with longer distances.
According to Pan Jian-Wei, a quantum physicist at the University of Science and Technology of China and leader of the satellite project, it would take hundreds of years to send a single key bit successfully from Beijing to Shanghai using a single fiber connection. The maximum practical range for a fiber link is less than 100 miles, and the eastern China network employs more than 30 “trusted” nodes, each of which decodes and stores keys locally before initiating a QKD session with its nearest neighbor.
Even with short-range transmissions, the rate at which keys can be transmitted remains orders of magnitudes below the rates needed to transfer bulk data. Ideally, QKD would be used to support the concept of the one-time pad, where no key bit is ever used twice. This reduces the probability of decryption using brute-force methods practically to zero. However, low practical key rates mean that practical applications use the same key repeatedly to support the transmission speeds needed for commercial applications. Ribordy says a typical use-case is to use QKD to send frequent key updates to support symmetric ciphers such as AES. “You update the key, say, 10 times per minute. Very basically, you limit the vulnerability of a particular key being broken,” he explains.
John Leiseboer, CTO of Australia-based QuintessenceLabs, says: “When it comes to the one-time pad, I think that’s a great place to go. But then again, I think, do we have to get to the one-time pad? It’s better if there is no practical attack possible at all, but there are always practical things you need to take into account. You will always be open to weaknesses. I work with ways of trying to engineer a solution and work within the bounds of what’s feasible and practical.”
The need to decode and store key bits at each trusted node increases the vulnerability of QKD-based networks, though these risks are no higher than they are for existing networks owned by telecom operators. Ribordy says, “If you think about telecom operators deploying QKD networks based on trusted nodes, they already have suitable secure facilities. It is relatively easy to guarantee the physical security assumption.”
One way to reduce the risk of relying on trusted nodes is to introduce quantum repeaters at each relay point. Such repeaters do not need to resolve the quantum states of photons as they are received. They allow the signal to be refreshed and passed on directly without having to store the key bits temporarily. Researchers have built devices that may be able to act as quantum repeaters, but they are still far from practical and would demand a change of equipment to use quantum entanglement to encode data. This is more difficult to achieve compared to the polarization-based technology of today’s single-photon QKD systems.
A set of repeaters can, in principle, swap entangled states between pairs of photons that were created on separate links. By performing multiple swapping procedures, repeaters extend an entanglement across the entire length of the network. The swapping is achieved at the cost of further drops in data rates, because not every attempt to swap is successful. However, the performance penalty is likely to be far lower than that encountered with longer runs of fiber.
“I would dearly love to see a practical quantum repeater developed,” Leiseboer says. “It would be a significant game changer. But it’s a relatively long-term option, and we don’t know when or whether it’s going to happen. Until we get there, we have to use other means.”
Ribordy adds, “Unconditional security through quantum repeaters would be nicer to achieve. But for the first generation of deployment, it’s feasible to use trusted nodes combined with satellites. We can deploy optical fiber on continents, and then bridge across continents using satellites. That enables the first wave of quantum communications.”
By demonstrating QKD working over longer distances, the Chinese projects have helped reinvigorate interest in the technology, Ribordy says.
In February 2017, six months after the launch of the Chinese Micius satellite used to perform quantum-communications projects, the European Space Agency (ESA) held a meeting to hear pitches for its Scylight satellite-based QKD project. “It’s a bit too bad that we had to wait for the Chinese to do it to pique the interest of the ESA in QKD,” laments Ribordy.
Both ID Quantique and QuintessenceLabs are working with the space and defense agencies of Switzerland and Australia, respectively, on their own experiments into space-borne QKD networks. Work on QKD has yielded other results that will be useful across cryptography, whether it is based on quantum or classical communications.
“We are developing techniques and subsystems that can be used now in real products that are not tied to QKD. For example, we now have a quantum random-number source that’s entirely as a result of the QKD effort,” Leiseboer says.
The next steps for QKD proponents are to build on the existing experiments to demonstrate the effectiveness of QKD and to start bringing the cost of the relay equipment down. Leiseboer notes, “There is no short-term major breakthrough that needs to be achieved. It’s about reducing the cost and making it smaller.”
Bennett, C. H. and Brassard, G.
Quantum cryptography: Public key distribution and coin tossing Proceedings of the IEEE International Conference on Computers, Systems and Signal Processing, Vol 175, p 8. New York (1984)
Liao, S-K. et al.
Satellite-to-ground quantum key distribution Nature (Accelerated Preview, August 2017). DOI: 10.1038/nature23655
Sasaki, T., Yamamoto, Y., and Koashi, M.
Practical quantum key distribution protocol without monitoring signal disturbance Nature, Vol 509, p475 (2014). DOI: 10.1038/nature13303
Pirandola, S., Laurenza, R., Ottaviani, C., and Banchi, L.
Fundamental limits of repeaterless quantum communications Nature Communications, 8:15043 (2016). DOI: 10.1038/ncomms15043




Join the Discussion (0)
Become a Member or Sign In to Post a Comment