The Upper Layers of the Internet
November 2018 - Vol. 61 No. 11
Features
Self-Reference and Section 230
The Gap in CS, Mulling Irrational Exuberance
The EU’s Controversial Digital Single Market Directive
How Machine Learning Impacts the Undergraduate Computing Curriculum
Using Any Surface to Realize a New Paradigm for Wireless Communications
Introducing Communications’ Regional Special Sections
Welcome to the China Region Special Section
Quantum Communication at 7,600km and Beyond
The Future of Artificial Intelligence in China
Consumers, Corporations, and Government: Computing in China
Regional Computing Culture and Personalities
Can China Lead the Development of Data Trading and Sharing Markets?
Exploiting Psychology and Social Behavior for Game Stickiness
People Logistics in Smart Cities
Cloud Bursting for the World’s Largest Consumer Market
Fintech: AI Powers Financial Services to Improve People's Lives
Is Last-Mile Delivery a ‘Killer App’ for Self-Driving Vehicles?
Video Consumption, Social Networking, and Influence
Will Supercomputers Be Super-Data and Super-AI Machines?
Corp to Cloud: Google’s Virtual Desktops
Research for Practice: Knowledge Base Construction in the Machine-Learning Era
Tracking and Controlling Microservice Dependencies
Skill Discovery in Virtual Assistants
Modern Debugging: The Art of Finding a Needle in a Haystack
Software Challenges for the Changing Storage Landscape
Technical Perspective: Backdoor Engineering
Where Did I Leave My Keys?: Lessons from the Juniper Dual EC Incident
Technical Perspective: Making Sleep Tracking More User Friendly
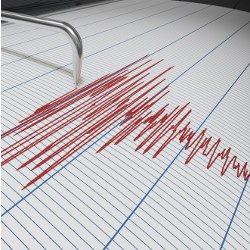
LIBS: A Bioelectrical Sensing System from Human Ears for Staging Whole-Night Sleep Study