January 2013 - Vol. 56 No. 1

Features
Computer Science Is Not a Science
How We Build Things: <i> . . . and Why Things Are 90% Complete</i>
Beyond Location: Data Security in the 21<sup>st</sup> Century
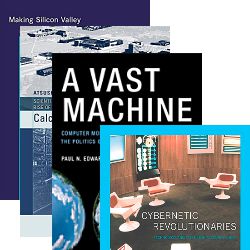
Five Lessons from Really Good History
Browser Security: Appearances Can Be Deceiving
The Web Won’t Be Safe or Secure Until We Break It
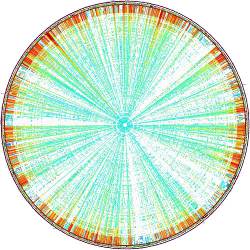
Human Mobility Characterization from Cellular Network Data
Computer Security and the Modern Home
Technical Perspective: Visualization, Understanding, and Design
Illustrating How Mechanical Assemblies Work
Technical Perspective: Finding People in Depth
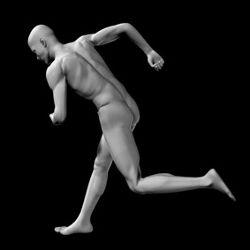
Real-Time Human Pose Recognition in Parts from Single Depth Images
Future Tense: Share My Enlightenment