Security and Privacy
We Need to Focus on How Our Data Is Used, Not Just How It Is Shared
Can Crowdsourcing Rescue the Social Marketplace of Ideas?
To Regulate Tech, Nullify Click-Through Contracts
Finding the Right Mix of Creativity and Technology
Face It, Self-Driving Cars Still Haven’t Earned Their Stripes
Duped No More: Navigating the Maze of Social Engineering Schemes
Automated Tests Are the Safety Net
Mixed Abilities and Varied Experiences: A Group Autoethnography of a Virtual Summer Internship
Teaching the FATE Community about Privacy
The Carbon Footprint of Artificial Intelligence
Voice in the Machine: Ethical Considerations for Language-Capable Robots
Technical Perspective: Pandemics, Remote Work, and Accessibility
Technical Perspective: Can We Uncover Private Backbone Infrastructures?
A Manifold View of Connectivity in the Private Backbone Networks of Hyperscalers
Improving Computing Education Research through Valuing Design
AI and Society: Ethics, Trust, and Cooperation
Why You Should Be Able to Make Your Own Individualized, Digital Nano-Currency
A Computational Inflection for Scientific Discovery
A Tale of Two Markets: Investigating the Ransomware Payments Economy
GenAI: Giga$$$, TeraWatt-Hours, and GigaTons of CO2
Concerns Grow about MFA Bypass Attacks
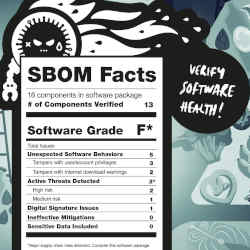
A Nested Inventory for Software Security, Supply Chain Risk Management
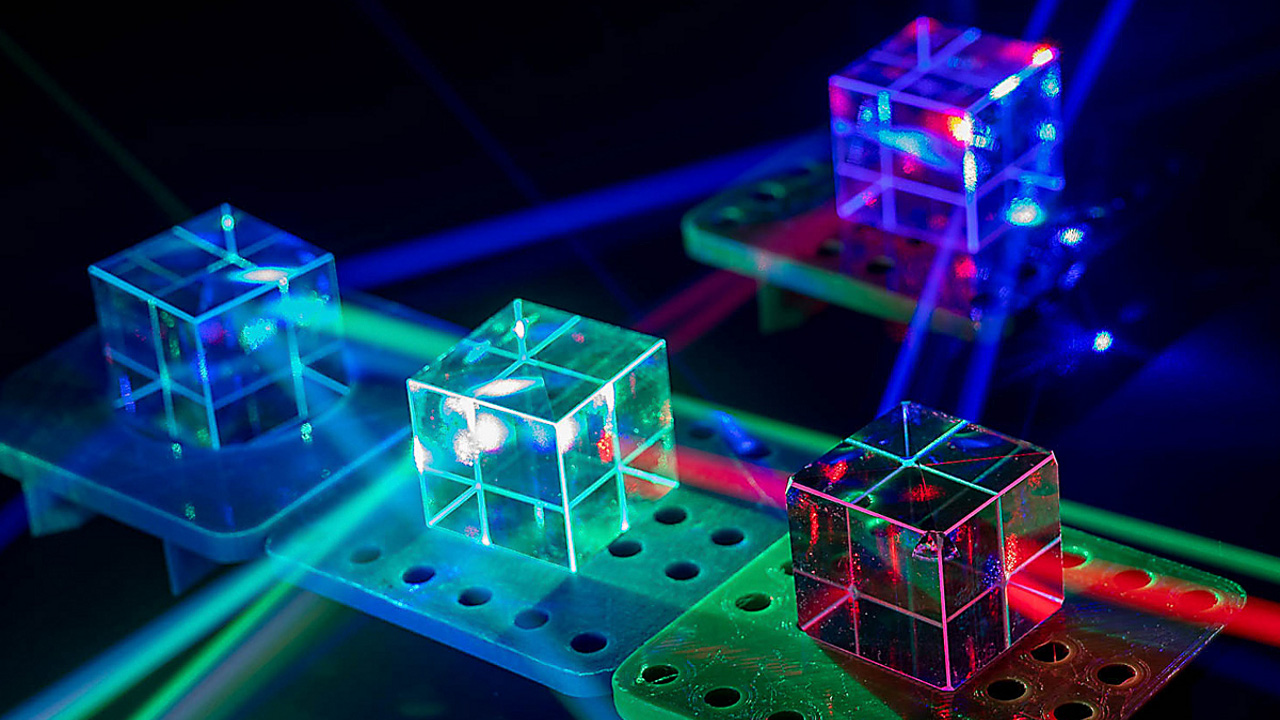
Accelerating Optical Communications with AI
Shape the Future of Computing
ACM encourages its members to take a direct hand in shaping the future of the association. There are more ways than ever to get involved.
Get InvolvedCommunications of the ACM (CACM) is now a fully Open Access publication.
By opening CACM to the world, we hope to increase engagement among the broader computer science community and encourage non-members to discover the rich resources ACM has to offer.
Learn More