Boolean Satisfiability: Theory and Engineering
March 2014 - Vol. 57 No. 3

Features
Develop Research Culture in the Arab Middle East
Capturing and Structuring Data Mined from the Web
Why Software Engineering Courses Should Include Ethics Coverage
The Impact of the United Nations Convention on the Rights of Persons with Disabilities
How to Build a Bad Research Center
Eventually Consistent: Not What You Were Expecting?
Scaling Existing Lock-Based Applications with Lock Elision
Making Parallel Programs Reliable with Stable Multithreading
Using Targeted Conferences to Recruit Women Into Computer Science
Big-Data Applications in the Government Sector
In the same way businesses use big data to pursue profits, governments use it to promote the public good.
Technical Perspective: Smartphone Security ‘Taint’ What It Used to Be
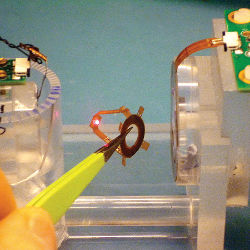
TaintDroid: An Information Flow Tracking System For Real-Time Privacy Monitoring on Smartphones
Puzzled: Solutions and Sources