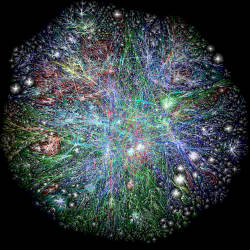
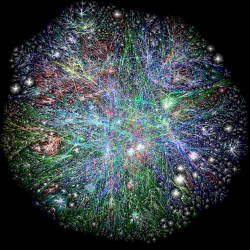
People have predicted the Internet’s death by traffic since its origin. Small protocol changes have prevented congestive collapse throughout the years, even as the Internet’s fundamental host-to-host structure has remained unchallenged. But that may need to change soon, as an increasing number of sensors, phones, and other mobile devices connecting to the Internet threaten the network’s security and reliability.
The growth is staggering: a Visual Networking Index Mobile Forecast by Cisco Systems estimates that mobile traffic worldwide will increase at a rate of 66% per year, or almost three times that of fixed-IP (Internet Protocol) machines, over the period 20122017. The nature of the data is also changing, pulled on one side by monolithic files like movies, and on the other by active streams of small data such as those created by field sensors. Security issues compound the problem, as the data travels in a network that protects the endpoints rather than the data packets themselves. Efforts to scale the Internet will need to take such scaling and security effects into account to preserve its usefulness for years to come.
Several active projects are attempting to design a "future Internet" to meet the challenges of the 21st century, including responding to the effects of mobile-device growth. While their implementations vary, they generally share the assumption that yesteryear’s host-to-host networking design is no longer appropriate in a world where devices change locations, network connections, and configurations frequently.
One large-scale coordinating effort can be found at the U.S. National Science Foundation (NSF), which announced its Future Internet Architectures (FIA) program in 2010, in addition to announcing funding for three projects that propose ways to augment (and possibly replace) parts of the Internet in ways that are likely to benefit device access directly. (A fourth "NEBULA" project focuses on creating a reliable cloud utility; a fifth, "ChoiceNet," examines economic issues that are relevant to all these projects.)
The FIA program has a long pedigree. It grew out of a "Future Internet Design" program that funded more than 50 projects between 2004 and 2009; that, in turn, came from the agency’s network architecture work reaching back to NSFNET, the National Science Foundation Network, in the mid-1980s. According to Darleen Fisher, program director for Networking Technology and Systems (NeTS) at the NSF, some of the current problems find their origins in requirements of that early network. "The purpose of NSFNET was to connect researchers and facilities," she said. To speed adoption, "The early NSFNET team decided not to require security, because they were concerned that one more requirement might be the final straw that would keep universities from connecting to it." Such decisions, while appropriate at the time, would come back to haunt Internet users years later.
From Host-Centric to Content-Centric Networking
One family of emerging solutions focuses on the purpose and content of data, rather than on where it lives. The approach is known as information-centric networking (ICN), a topic in which "there are easily two or three dozen projects going on," according to Glenn Edens, research director in the Computer Science Laboratory at PARC. His group has developed a protocol specification of ICN named Content-Centric Networking (CCN), and with it an open-source reference implementation, CCNx. "That codebase is used by a couple of hundred institutions," said Edens. "It’s been ported to around three dozen architectures that we know of. Today, it is running on everything from Raspberry Pis and BeagleBoards and tiny home routers, all the way up to really large cloud switches."
Another project that originally used the CCNx code is the Named Data Networking (NDN) project, an FIA-funded effort led by the University of California, Los Angeles (UCLA) with cooperation from eight other universities and PARC. According to Lixia Zhang, professor of computer science at UCLA and a member of the board of the Asia Future Internet Forum, the NDN project aims to create ICN-style applications "to meet actual needs."
One such need was found in an unlikely place—the University’s School of Theater, Film and Television. Said Zhang, "When one of our investigators tried to automate stage control stuff in the early 2000s, he noticed that there was a big gap between what application developers would like and what the Internet actually provides. When he wanted to turn on the left upper-corner lights, the network said, ‘give me a packet with an IP address and port number, so I can send it to the destination,’ but he did not know or care about IP addresses or port numbers; he wanted things to happen according to the application’s semantics."
NDN claims to accomplish this by naming data rather than endpoints, using a human readable and hierarchical name, much like a URL. A user requests data by sending out an "Interest packet;" for example, /tvchannel/videos/favoriteshow/season1episode4.mpg/2ndAct. Routers note the interface of the Interest packet and forward it according to information in a "Forwarding Information Base" (FIB), which is dynamically populated (FIBs are unlike today’s routers in that they store name prefixes instead of IP prefixes). When the Interest packet reaches a location that holds the requested data, that location returns the data to the user along the same path. The data packet contains the data’s name, its content, and a signature that binds the name to the data.
This architecture removes redundant retrieval of the same content. Since each data packet carries both a name and a signature, it can be cached in various points along the path. The project claims this facilitates content distribution, multicasting, transfer over poor connections, and support for mobility and disruption-tolerant delivery. Zhang claims that, regardless which node supplies the data, NDN gives packets provenance and integrity by binding their names and data together with the signatures.
Billions of Tiny, Moving Targets
In contrast to NDN’s hierarchical naming structure, the FIA-funded MobilityFirst project describes a two-part naming system for "network objects," which could be devices, people, internal networks, or even content. First, each network object is given a human-readable name; then, a name certification service (NCS) connects each of these to a Globally Unique ID (GUID). These GUIDs are unstructured and, as such, are unlike either IP addresses or MAC addresses. The result, according to MobilityFirst literature, is a network better suited for the billions of phones, wireless sensors, vehicles, and machines that have no fixed location.
When a network object becomes active, a global name resolution service (GNRS) dynamically binds its GUID to its current network address, or even to multiple network addresses.
Dipankar Raychaudhuri, the project’s lead investigator and director of the Wireless Information Network Laboratory (WINLAB) at Rutgers University, claims that several of MobilityFirst’s special benefits come from the combination of a new naming procedure and a new routing layer. "We have optimized the routing layer to do new things like network storage functionality," he said, "and it does multi-homing and multi-casting very efficiently. You could also put the [named] part of our architecture on top of ordinary IP for backward compatibility, but then you do not have the benefit of some of MobilityFirst’s features such as storage routing, which can be useful for content and cloud applications."
MobilityFirst bindings between names and numbers can be domain-specific. "The name certification service is somewhat similar in spirit to what ICANN provides for domain names," said Raychaudhuri, "but there’s no central authority, so you can accept any NCS that you trust. For a device that’s part of my car, the NCS could be the auto manufacturer."
Raychaudhuri believes the use of practically inexhaustible GUIDs will prevent the sort of unstable and "roundabout" process now needed to get mobile devices on the Internet. "If you have a smartphone, you get a private IP address from the cell provider, then there is a public IP address in a gateway at the boundary of the cellular network. That gateway is a potential bottleneck or single point of failure. With MobilityFirst, a mobile device does not have to go through the gateway. No matter what network you are connected to, the global name resolution in MobilityFirst will find your current location."
Addressing Unknown Unknowns
MobilityFirst prioritizes issues of mobile accessibility; NDN focuses on content. A third FIA-funded project takes an agnostic approach in forecasting the Internet’s needs. The eXpressive Internet Architecture (XIA) project divides Internet players into "principals" such as hosts, content, services, and users. While identifying such current principals, it acknowledges that tomorrow’s Internet may have other types of principals, and is built to adapt when they appear. Whatever the principal type of a network resource, XIA describes a way to reach it directly through a new eXpressive Internet Protocol (XIP). As principal investigator and Carnegie Mellon University professor Peter Steenkiste said, "If we look forward to 10 years from now, are we really sure that content and services will be the hot commodity? That is absolutely not clear: there might be a change in the types of entities that people will want to send."
Steenkiste described how an XIA requestor packet could get a satisfying response even when points on the network do not understand its new-form destination type. "The current Internet thinks of packets as having a destination address with one type of ID, such as an IP address," he said. "In XIA, I would request a piece of content with a Content ID. But I would realize that not all Internet routers recognize that, so I would include a second ID, which is a Host ID. If the router does not understand the first one, it can look at the second or third, and it will basically act on the first one that it recognizes. For backward compatibility, that last ID could be an IP address."
"If we continue to solve the problems that we have set out to solve, you should be able to interact with the content network just like you interact with the Web."
For security, XIA borrowed an idea from a prior NSF-funded project, Accountable Internet Protocol (AIP): incorporating a cryptographic ID in addresses so they can be authenticated through a public-private key challenge. Steenkiste says the project uses this scheme so it does not have to rely on key-management infrastructure, as both NDN and MobilityFirst do.
He also explained how such embedded authentication allows duplication not only of content, but also of dynamic services like entire websites. "You could replicate services using a public key, but then you could end up replicating a private key on a lot of devices. In XIA, there is one public-private key pair for the global service; then, there are basic public key pairs with each instance. They are all tied together with a certificate that is issued by the service’s owner, not a global certificate authority. The instances cannot hand the service off to others because they cannot sign for it: their private keys are not authoritative."
The Growth of Everything
Three themes are consistent in these projects’ approaches: the Internet is growing in terms of not only numbers, but also diversity; the current seven-layer OSI model needs adjustment to move it away from host-centric networking; security must be a first-order concern in every data transaction, not only at the endpoints. These changes require fundamentally different ways of thinking about networking from those currently in play.
Yet for Internet users, the basic experience should remain the same. As PARC’s Edens put it when speaking of CCN, "The seven-layer model is getting pretty darn tired, but if we continue to solve the problems that we have set out to solve, you should be able to interact with the content network just like you interact with the Web. You ask for content, and you get it back —you do not care whether it is cached or comes from the original publisher. But with intelligent routers, you can have things like dynamic rerouting, error recovery, and broadcasting. You can put all these functions into the network as services."
Or, as NSF’s Fisher noted, "We never expected the FIA projects would replace the current Internet, although some project evangelists are motivated by that as a holy grail. In either case, these projects can have a very large impact. That is very exciting."
Further Reading
NSF Future Internet Architecture Project, National Science Foundation, http://www.nets-fia.net
VNI (Visual Networking Index) Mobile Forecast Highlights, 2012-2017, Cisco Systems, Inc., http://www.cisco.com/web/solutions/sp/vni/vni_mobile_forecast_highlights/index.html.
Raychaudhuri, D., Nagaraja, K., Venkataramani, A.
MobilityFirst: A Robust and Trustworthy Mobility-Centric Architecture for the Future Internet. Draft, August 2012. http://mobilityfirst.winlab.rutgers.edu/documents/MobilityFirst_paper_MC2R_v10.pdf
Zhang, L., Estrin, D., Burke, J., Jacobson, V., Thornton, J. D., Smetters, D. K., et al. (2010)
Named Data Networking (NDN) Project. PARC Tech Report 2010-003 NDN-0001, PARC.
Han, D., Anand, A., Dogar, F., Li, B., Lim, H., Machado, M., et al. (2012)
XIA: Efficient support for evolvable internetworking. Proc. 9th USENIX NSDI.



Join the Discussion (0)
Become a Member or Sign In to Post a Comment