Since its inauguration in 1966, the ACM A.M. Turing Award has recognized major contributions of lasting importance to computing. Through the years, it has become the most prestigious award in computing. To help celebrate 50 years of the ACM Turing Award and the visionaries who have received it, ACM has launched a campaign called “Panels in Print,” a collection of responses from Turing laureates, ACM award recipients and other ACM experts on a given topic or trend.
ACM’s celebration of 50 years of the ACM Turing Award will culminate with a conference June 23–24, 2017, at the Westin St. Francis in San Francisco. This unique event will highlight the significant impact of ACM Turing laureates’ achievements on computing and society, to look ahead to the future of technology and innovation, and to help inspire the next generation of computer scientists to invent and dream.
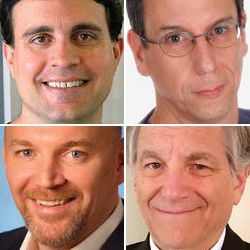
For our second Panel in Print, we invited 2002 ACM Turing laureate Len Adleman, 2014 ACM Prize in Computing recipient Dan Boneh, 2015 ACM Grace Murray Hopper Award recipient Brent Waters, and ACM Fellows Patrick McDaniel and Paul van Oorschot to discuss current issues in cybersecurity.
The cybersecurity discipline has developed rapidly. Do you think we are staying ahead of, or falling behind, the threats?
LEN ADLEMAN: I think that we are behind. Cybersecurity is a cat-and-mouse game. There can never be a final victory. The Internet is developing so quickly, along so many paths, that while we address current problems, we cannot even anticipate those that are emerging.
BRENT WATERS: In the research realm of cryptography, we have made significant leaps in the past 15 years in terms of which new functionalities we can realize. These include solutions to problems such as identity-based encryption, attribute-based encryption, and fully homomorphic encryption, and potentially can realize an exciting primitive called indistinguishability obfuscation.
Where we seem to be facing problems is filling in the gap between sound cryptography and sound deployments. These deployments can fail for any number of reasons from bad software implementation, to poor design of new cryptography, to use of legacy cryptographic protocols.
What do you see as the top cybersecurity threats in 2017 and why?
DAN BONEH: Social engineering attacks remain one of the top cybersecurity issues in 2017. Phishing and related attacks are still effective at stealing user credentials. Targeted emails continue to be effective at fooling end users into installing unwanted software such as adware, malware, or ransomware. These are common occurrences, and are often the easiest way to gain a foothold on a targeted system. Two-factor authentication and application whitelisting can make the attacker’s job harder. They are tools to be used as part of a broad defense strategy.
PATRICK MCDANIEL: There’s been an interesting transition of threats and attacks over the last 10 years, and what we’re seeing more frequently is professional attacks that more effectively monetize the vulnerabilities in computers. In particular we have seen the rise in things like ransomware, which has become a very serious problem for businesses, government agencies, and organizations that don’t have full-time professional cybersecurity staff.
Just looking at what is happened over the last six months in the U.S., it’s clear that misinformation has become a major weapon in the cyber-criminal’s arsenal. I think we will see even more attacks where misinformation is used to try and shape public policy, sway public opinion or even to alter people’s behaviors. Obviously the use of misinformation is nothing new—we’ve seen it before with stock market manipulation, etc.—but I think we’re going to see much newer and inventive uses of misinformation as a means of cyberattack.
PAUL VAN OORSCHOT: It’s a long-standing problem: software vulnerabilities allowing compromise of user devices and remote control of these compromised machines. This is easily addressed in theory, but harder to fix in the real world. Problems stem from long-ago and deeply entrenched architectural choices in operating systems; use of software applications which favor rich functionality over conservative design; and the freedom allowing users to download and install software with a single click makes us all vulnerable to being socially engineered to install software without any sound evidence or knowledge of what the software will do. It’s not likely that we will be able to retrain 10 million software developers, nor to motivate them to voluntarily spend extra time on security when the economic benefit of doing so falls to others. That’s an economics of information security challenge—as is that fact that historically, almost all software is sold on an as-is basis without liability for consequences.
Why are cyberthreats/attacks becoming more sophisticated with each passing year?
BRENT WATERS: One can attribute this to two basic reasons. First, technology in general becomes better and more sophisticated over time. One would expect the sophistication of cyberattacks to also flow in that same direction. Another important factor is that with more and more data stored on computing devices, the value in launching attacks increases. For example, there have been multiple attacks that exposed private communications and photos of celebrities. Ten years ago, without smartphones, these photos either wouldn’t be taken or wouldn’t be accessible. As another example, in this election cycle we have seen that attacks (for example, the DNC emails) have the potential to shake up organizations and possibly shift outcomes in elections. This type of power will not only interest the usual attackers, but will also attract extremely well-funded state sponsored adversaries.
With the public more concerned about cybersecurity than ever before, what should be the top cybersecurity priorities for the new U.S. administration?
DAN BONEH: The highest priority for the new U.S. administration is to shore up the cyber defenses of government systems. Events like the 2015 attack on the office of personnel management that exposed the personnel records of over 21 million people, or the compromise of the IRS systems that may have exposed personal data from over 700,000 taxpayers, should not happen again.
PATRICK MCDANIEL: Our federal IT systems, as we have learned repeatedly, are very much antiquated, due to things like underfunding. But if our society is to become more secure, then we need to focus on updating and fixing those federal systems. One way in which we could do this would be for the current administration to immediately prioritize creating a national two-factor authentication system, either for federal employees or even more broadly. Although that sounds somewhat boring, I think that is the single simplest thing we can do to reduce the threats against the information systems we have in this country. A good friend and colleague of mine, Farnam Jahanian, the Provost of Carnegie Mellon University, has said, “We are not good at doing the easy things, and we need to get better at them.”
What are the biggest challenges faced by industry in defending against cyberattacks, and what technologies/approaches can help them overcome these challenges?
LEN ADLEMAN: I think the issues raised in the question transcend industry. From my forthcoming book, Memes: How Genes, Brenes and Cenes Shape Your Life and Will Shape the Future of Humanity:
We will soon see religions, nations, and economies rise and fall in cyberspace. These entities will be no less powerful and have no less impact on our lives than their current “brick and mortar” counterparts. Political, economic, and even military power will be diffuse; the physical locations of like-minded people will be less important than their numbers and connectivity.
If the U.S., Russian, and Chinese governments are not working on black hat programs that, in the event of war, will knock out the computational infrastructure of the other two, they aren’t doing their jobs. Such programs are weapons of mass destruction, and, if used, the death toll could be colossal. A first world country with no computational infrastructure is a country with no economy, no food, no power and ultimately not a country at all.
“The Internet is developing so quickly, along so many paths, that while we address current problems, we cannot even anticipate those that are emerging.”
What are your biggest security concerns as they relate to the influx of connected devices in the Internet of Things (IoT)?
PATRICK MCDANIEL: When it comes to IoT and the future of security, I have a vision of two possible futures. The first scenario comes at a significant cost. But I believe this to be the more optimistic future, because we will understand the trade-off between cost and value, and we’re going to pay for it so we can live in a world in which we have much better security than we do today.
The second, and in my view, the more pessimistic scenario is a world in which we have just become used to insecurity. There is a kind of really toxic resignation among some members of the cybersecurity research community as well as industry and government, that today’s systems are unfixable and that we don’t have the technology, time or resources to make ourselves more secure. I think this is a particularly dim and uncomfortable scenario, not only because the kinds of benefits we see from technology would be greatly diminished, but our potential for changing life on this planet—from healthcare, to society, to communications, to quality of life to energy efficiency, to protecting the environment—will be vastly diminished, if we just accept insecurity.








Join the Discussion (0)
Become a Member or Sign In to Post a Comment