Within minutes of arriving at NSA headquarters, I had already aggravated my host, Lydia. It started the moment I offered to get her a soft drink only to realize I had no money to pay for hers—or even for my own. As she grudgingly paid for both, her irritation only grew as I explained I was so accustomed to the free food and drinks at Ubatoo I didn’t realize some offices were still so antiquated in their treatment of employees.
Ubatoo.com, my former employer, epitomized Silicon Valley. Early on, it set the standard for perks and eccentricities and had grown to be synonymous with the Internet itself. Write an email message, update your personal status, buy something online, watch a video, upload a picture, search a secret desire you’ve never shared with anyone—Ubatoo made it all possible.
Today’s meeting was intended as a brainstorming session on deploying Ubatoo’s Web-ranking algorithms to help NSA rank "suspects" on its evergrowing watch lists. Lydia, however, was in pure selling mode.
"We live in a connected world," she said, the moment Doug, her boss, was seated. "It’s not just about the people you say are your ‘friends’ but about all the connections we infer."
An ode to minimalism, her first slide was a white screen with two tiny dots in the center. "One is you, Doug," she said. "The other is your daughter, Deirdre. When you make a phone call to her, we connect the dots." She tapped a key and a connecting line materialized.
"We know you write her an email message every day." The connection between them grew thicker.
"Deirdre calls and texts her boyfriend, Josh, right?" A dot for Josh emerged, already connected to Deirdre. "He’s taking a course." A line between Josh’s dot and his professor, Dr. Kione, appeared.
"And this Kione teaches political media by examining half a dozen Web sites, one of which is a known extremist breeding ground." Six new dots popped up, one for each site, five black, one red, indicating "under surveillance," all connected back to Kione.
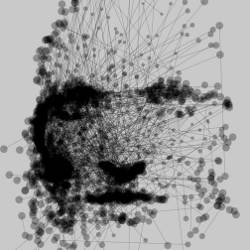
"Now it’s just a game of ‘connect the dots’; it’s unlikely he supports the extremist groups he’s encountered, but he might have mentioned them in class." Like a slow drip across the screen, the red seeped outward from the lone red dot, flowing through all the connections it touched. "It’s possible Josh talked about it with Deirdre." The red continued its crawl through the thick and thin connections between other dots along the way, getting fainter with each one. "It’s unlikely she would talk about it with you. Unlikely, but not impossible." The red had almost disappeared by the time it reached back to Doug’s no-longer pristine black dot.
"You’re not terribly red, so you’re okay," said Lydia, "but imagine we repeated this procedure with every Web site you visited, every person you called or emailed, every product you purchased—each represented here by a tiny dot, connected by thick and thin lines back to you. Some connections will inevitably link you to persons of interest, to things and events we monitor. You’ll be connected to all those little red dots we’ve worked so hard to identify."
Doug was skeptical. "There would be billions of dots and connections. Where would all this information about me, or anyone else, come from?"
I started to answer, but Lydia jumped in. "That’s the greatest irony of all. Nobody would let us have it, of course, but everyone, I mean everyone, just gives it to Ubatoo." It was a well-rehearsed line, every word dripping with satisfaction. "Each action, email message, trip, search, thought—all there, stored on the company’s servers somewhere."
I wondered if I needed to say what should have been obvious, especially with the daily privacy fears and fiascos in the news. Ubatoo would never grant them access to the data, its most cherished possession. Only the thought of him spouting some cliché like, "Don’t worry, kid. It’s above your pay grade," kept me silent.
"That makes life easier," Doug said with inexplicable relief.
Instantly, Doug realized his inadvertent comment may have revealed more than he intended. Quickly changing the topic, he turned to me, saying, "So you’re the one from Ubatoo who came up with all this? Does it really work?"
"Yes," I said, grateful for the chance to speak, "but not the way you…"
Lydia cut me off again. "Just take a look at this small example, Doug." A few red dots were now floating among thousands of black ones. An impenetrable jumble of thick and thin lines—connections—blanketed the screen like cartons of spilled toothpicks in a puzzle designed for Rain Man.
The "red influence," as Lydia called it, perhaps a reference to the Cold War, was now unleashed. We all watched as the red permeated the page. "Like a biological infection through water pipes," she said. "You see, if you’re connected to enough bad things, at some point, your dot is going to glow bright red, too. And when it does, we’ll know you’re worth the resources to investigate. Just like ranking Web pages at Ubatoo, it all comes down to your connections."
Lydia was on a roll. "Let’s zoom into this person’s red dot. You can see the books he’s read. His connections to them made them red, too. See how some are brighter than others? Those were read by others on our lists as well. Even the soft drinks we’ve seen him drink are all redder because of him. It’s all in our graph."
"Just like ranking Web pages at Ubatoo, it all comes down to your connections."
"Zoom in on the drinks," Doug said, amused. "Let’s see which are, um, suspicious."
Lydia did as she was told, despite regretting her choice of example. On the screen were a dozen circles, each its own shade of red. She worked her way down the list until she got to the reddest of all—the most suspicious in the set. She breathed the name reverently and stepped back from the table to let the discovery sink in.
I couldn’t take it anymore. "No. No. You can’t just…"
This time it was Doug who cut me off, "Relax, Stephen, I get it. Of course the system doesn’t work for drinks." As I began to ease back in my chair, Doug began issuing commands to Lydia. "Use this to put together a list of the most suspicious people, books, Web sites, music, whatever you can think of, and send it to me ASAP!"
I think I mumbled something about how the system was never meant to be used like this. But what was the point? Doug was no longer paying attention; he stared at a sea of red circles, desperately trying to recall his daughter’s favorite soda, fearing he had just connected her to Lydia’s mess. Lydia was standing proudly at the head of the table with an enormous grin. Her gaze rested triumphantly on my hand, which was now, I realized, clutching a "most suspicious" choice of soft drink.



Join the Discussion (0)
Become a Member or Sign In to Post a Comment